Day 19 网页分析 - Web Application Analysis (Wapiti)
工具介绍
今天要介绍的工具叫做挖鼻涕Wapiti,是用来扫描网页的安全性,以黑盒的方式,也就是在不了解网页内部如何实作的状况下,模拟真实攻击者的手法。以下是Wapiti涵盖的侦测项目
- Database Injection (PHP/ASP/JSP SQL Injections and XPath Injections)
- Cross Site Scripting (XSS) reflected and permanent
- File disclosure detection (local and remote include, require, fopen, readfile…)
- Command Execution detection (eval(), system(), passtru()…)
- XXE (Xml eXternal Entity) injection
- CRLF Injection
- Search for potentially dangerous files on the server (thank to the Nikto db)
- Bypass of weak htaccess configurations
- Search for copies (backup) of scripts on the server
- Shellshock
- DirBuster like
- Server Side Request Forgery (through use of an external Wapiti website)
先来看一下用法
__ __ _ _ _ _____
/ / /\ \ \__ _ _ __ (_) |_(_)___ /
\ \/ \/ / _` | '_ \| | __| | |_ \
\ /\ / (_| | |_) | | |_| |___) |
\/ \/ \__,_| .__/|_|\__|_|____/
|_|
Wapiti-3.0.4 (wapiti.sourceforge.io)
[*] Be careful! New moon tonight.
usage: wapiti [-h] [-u URL] [--scope {page,folder,domain,url,punk}]
[-m MODULES_LIST] [--list-modules] [--update] [-l LEVEL]
[-p PROXY_URL] [--tor] [-a CREDENTIALS]
[--auth-type {basic,digest,kerberos,ntlm,post}]
[-c COOKIE_FILE] [--skip-crawl] [--resume-crawl]
[--flush-attacks] [--flush-session] [--store-session PATH]
[--store-config PATH] [-s URL] [-x URL] [-r PARAMETER]
[--skip PARAMETER] [-d DEPTH] [--max-links-per-page MAX]
[--max-files-per-dir MAX] [--max-scan-time SECONDS]
[--max-attack-time SECONDS] [--max-parameters MAX] [-S FORCE]
[-t SECONDS] [-H HEADER] [-A AGENT] [--verify-ssl {0,1}]
[--color] [-v LEVEL] [-f FORMAT] [-o OUPUT_PATH]
[--external-endpoint EXTERNAL_ENDPOINT_URL]
[--internal-endpoint INTERNAL_ENDPOINT_URL]
[--endpoint ENDPOINT_URL] [--no-bugreport] [--version]
wapiti: error: one of the arguments -u/--url --list-modules --update is required
这边用-o指定输出资料夹,-f指定输出格式为html,最後-u指定靶机上的页面
wapiti -o wapiti_result -f html -u http://192.168.1.86/dvwa
扫描过程会逐渐更新资讯,最後将结果产生一个报表输出到指定的位置
Note
========
This scan has been saved in the file /home/kali/.wapiti/scans/192.168.1.86_folder_335476bb.db
[*] Wapiti found 3 URLs and forms during the scan
[*] Loading modules:
backup, blindsql, brute_login_form, buster, cookieflags, crlf, csp, csrf, exec, file, htaccess, http_headers, methods, nikto, permanentxss, redirect, shellshock, sql, ssrf, wapp, xss, xxe
Problem with local wapp database.
Downloading from the web...
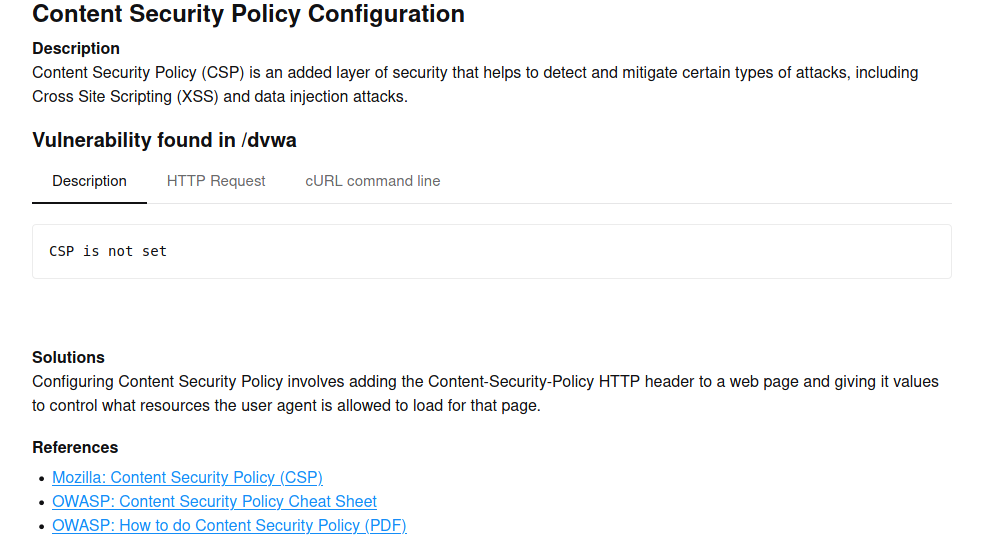
[*] Launching module csp
CSP is not set
[*] Launching module http_headers
Checking X-Frame-Options :
X-Frame-Options is not set
Checking X-XSS-Protection :
X-XSS-Protection is not set
Checking X-Content-Type-Options :
X-Content-Type-Options is not set
Checking Strict-Transport-Security :
Strict-Transport-Security is not set
[*] Launching module cookieflags
Checking cookie : PHPSESSID
HttpOnly flag is not set in the cookie : PHPSESSID
Secure flag is not set in the cookie : PHPSESSID
Checking cookie : security
HttpOnly flag is not set in the cookie : security
Secure flag is not set in the cookie : security
[*] Launching module exec
[*] Launching module file
[*] Launching module sql
[*] Launching module xss
[*] Launching module ssrf
[*] Asking endpoint URL https://wapiti3.ovh/get_ssrf.php?id=glpejm for results, please wait...
[*] Launching module redirect
[*] Launching module blindsql
[*] Launching module permanentxss
Report
------
A report has been generated in the file wapiti_result
Open wapiti_result/192.168.1.86_10042021_1417.html with a browser to see this report.
可以透过open来将输出结果以浏览器开启
open wapiti_result/192.168.1.86_10042021_1417.html
报表一打开就是所有被扫瞄出的问题的统计结果
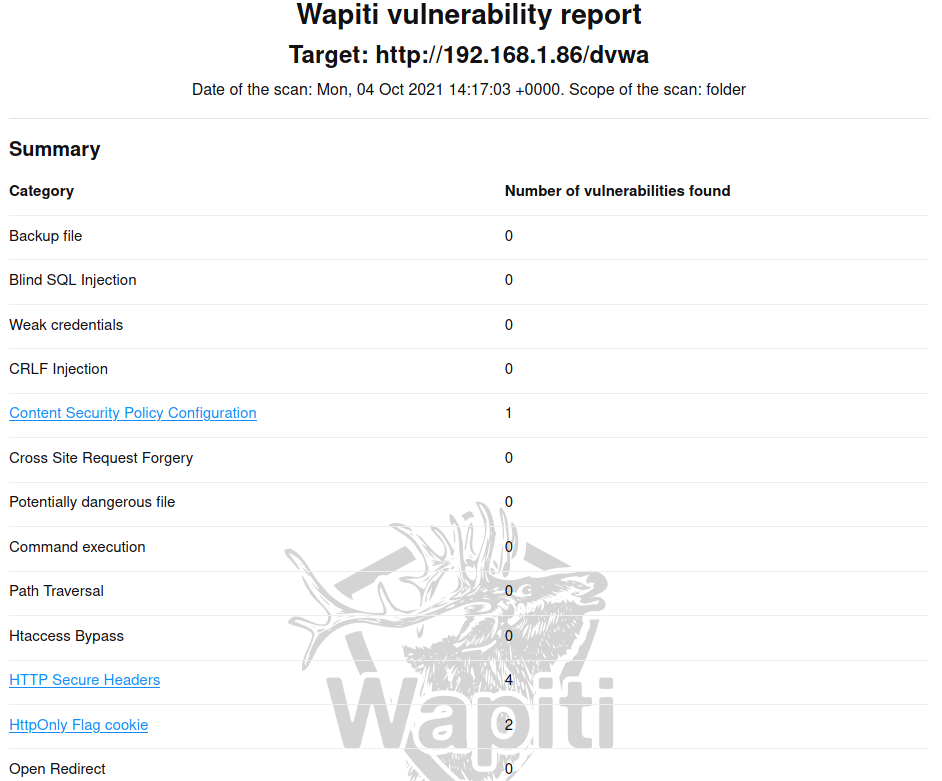
点击蓝底的超连结项目或是直接往报表下面卷动,都可以看到每个问题的详细资讯,而且还有建议的解决方案并且附上参考连结,感觉很不错
另外扫描过的目标,如果再扫一次,可能会发现第二次扫描很快就结束了,这是因为有一些资料已经先被记录下来,有点像cache的机制,但是是以sqlite的形式放在/home/kali/.wapiti之下
>>: [神经机器翻译理论与实作] 重新检视有无注意力机制的Encoder-Decoder
[Day11]程序菜鸟自学C++资料结构演算法 – 伫 列Queue
前言:上一篇结束了堆叠的实作,今天要来介绍新东西「伫列」。 伫列的特性:伫列和堆叠非常类似,同样都是...
110/12 - 把照片储存在Pictures/应用程序名称资料夹 - 2
Android 11开始把getExternalStoragePublicDirectory标记弃用...
Vue 动态组件
tags: Vuejs 动态组件 ✐ 动态组件可以帮助我们动态切换组件,例如在网页的多标签介面中常见...
【後转前要多久】# Day13 CSS - Display: Flex (vs Float)
当没有任何CSS时, HTML预设显示区块元素(block)方式都是 往下一行一行(row)长 HT...
Day 30 - 相关资源分享
本文将於赛後同步刊登於笔者部落格 有兴趣学习更多 Kubernetes/DevOps/Linux 相...